Many phishing email are designed poorly with bad grammar, etc. but others look legitimate enough for someone to click if they weren’t paying close attention. Cybercriminals are constantly updating their phishing techniques but there are a few consistent patterns in phishing emails, and if you can learn to identify them, you are much less at risk of clicking on one.
Set up your email software correctly
- update your software, if possible by activating the automatic update procedure;
- set your email program to disable automatic email previews;
- in the security settings in options, prohibit the automatic execution of ActiveX and plug-ins and downloads, either by disabling them or by requiring you to ask for permission;
- in a sensitive environment, read all messages in plain text format.
Set up two-factor authentication (2FA)
2FA is the most effective method for countering phishing attacks, as it adds an extra verification layer when logging in to sensitive applications. 2FA relies on users having two things: something they know, such as a password and user name, and something they have, such as their smartphones. Even when employees are compromised, 2FA prevents the use of their compromised credentials, since these alone are insufficient to gain entry.
Inspect the email sender address
Scammers will pretend to be a company you may know. However, the sender address will be different. For example, instead of laposte.fr they could be using lap0ste.fr or laposte.offre.fr.
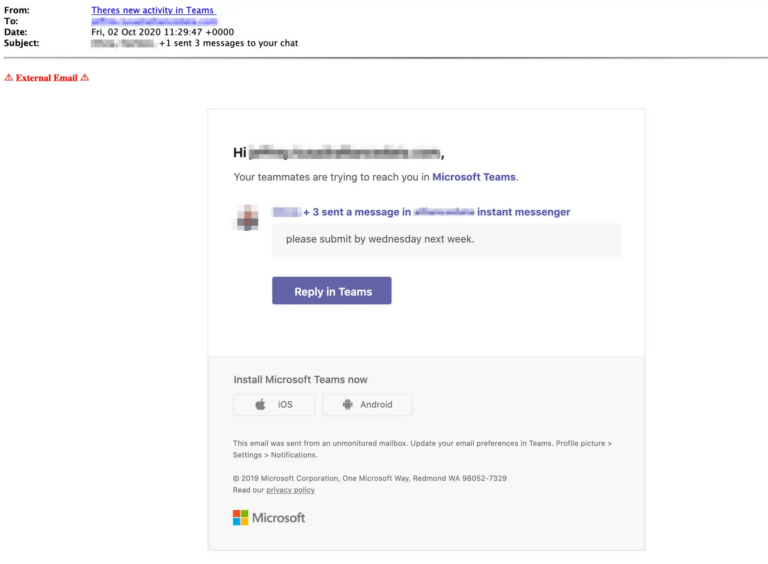
Hover over the link
If the email seems to be coming from a trusted source, hover over the link and verify that the domain matches who it should be. Indeed, when you hover over a link in Outlook or a web browser, a small window pops up to show you where the link really goes. If the real link doesn’t match the sender or doesn’t match what you expect, assume it is poisoned and don’t click it.
Don’t open suspicious attachments
Unexpected or suspicious email attachments should never be opened. These documents too often get past antivirus programs with no problem and they may execute a disguised program (malware, adware, spyware, virus, etc.) that could damage or steal your data. If in doubt, call the sender to verify.
When in doubt, close it out
If you’re not sure what to do with a suspicious email, the best thing is to just delete it. Consult with your manager or security IT staff to inquire about its validity.
To go further ...
Launch Phishing Security Test
There are a number of different techniques used to obtain personal information from users. As technology becomes more advanced the hackers techniques being used are also more advanced.
There is a common misconception that phishing is easy to spot and that only less technically-savvy people will fall victim but this is far from the truth. A phishing test holds the dual benefit of measuring your company’s risk and training your employees on what to look for in these attacks. Phishing Security Test familiarise employees with cyber threats to create a line of defence and push for a safer environment. In order to combat these threats, staff need to understand the telltale signs of an attack, the common techniques criminals use and what to do when they believe they’ve received a phish.